Start Doing.
Until You're Proud
Super Highway
What is displayed after this code runs?

A. "abcd" | B. "dcba" | C. "dcb" | D. ""
B. "dcba"
i starts at 4, decrements. Concatenates list[4]+list[3]+list[2]+list[1] = "dcba".
How do you best answer the question... what is the 'digital divide'?
The gap between those who have access to high-speed internet and modern technology and those who do not.
This divide is often driven by socioeconomic status, geographic location, or lack of infrastructure.
A student developed a program that works correctly but contains sections of duplicated code that appear in different parts of the program. What coding concept is most likely to make the program easier to maintain in the future?
Putting the duplicated code into a single procedure in such a way that allows the procedure to be called multiple times.
Which of the following best describes the World Wide Web?
A. The World Wide Web is another name for the network of interconnected networks known as the Internet.
B. The World Wide Web is the name for the set of protocols used to exchange information between devices connected to the Internet.
C. The World Wide Web is a system of linked pages and files that is accessed using the Internet.
D. The World Wide Web is a system used to identify users sending messages on the Internet.
C. The World Wide Web is a system of linked pages and files that is accessed using the Internet.
The World Wide Web is a system of linked pages and files. This system is accessed via the network of interconnected networks known as the Internet


A student's program uses a list to store the scores of 50 students. Why is using a list better than using 50 separate variables?
A.
It allows the program to iterate through all scores using a single loop, making the code easier to update and maintain.
Lists allow for scalable data processing and the use of iteration to handle many items with very little code.
An 8-bit color system is upgraded to a 10-bit color system. How many more unique colors can the new system represent compared to the old one?
768
The 8-bit system has 2^8=256 colors, and the 10-bit system has 2^10=1024 colors.
1024−256=768.
The following figure represents a network of physically linked devices labeled A through F. A line between two devices indicates that the two devices can communicate directly with each other. Any information sent between devices that are not directly connected must go through at least one other device. For example, in the network shown, information can be sent directly between devices B and C, but information sent between devices B and E must go through other devices.

A. If devices B and C fail, then information sent from device A cannot reach device F.
B. If devices B and E fail, then information sent from device A cannot reach device F.
C. If devices C and D fail, then information sent from device A cannot reach device F.
D. If devices D and E fail, then information sent from device A cannot reach device F.
Answer B Correct.
If devices B and E fail, device F will be completely disconnected from the network, preventing communication with device A.
Which of the following statements describe how an email could potentially compromise the security of a computing system? Select two answers.
I. The email could contain a link to a website that installs malware.
II. The email could contain a user's public encryption key.
III. The email could have an attachment that installs keylogging software when opened.
IV.The email could have been compressed using a lossy compression algorithm.
I. & III
Malicious links in emails can redirect users to websites that install malware, posing a security risk
Consider the expression (a MOD 2) + 1, where a is an integer greater than or equal to 0. Which of the following is a true statement about the expression?
A. The expression evaluates to 1 when a is even.
B. The expression evaluates to 1 when a is odd.
C. The expression always evaluates to 1.
D. The expression never evaluates to 1
Answer A Correct.
The expression (a MOD 2) is used to determine whether a is even or odd. It evaluates to 0 when a is even and evaluates to 1 when a is odd. Adding 1 to the expression causes it to evaluate to 1 when a is even.
A student wants to use a heuristic algorithm to solve a problem. In which scenario is a heuristic approach most appropriate?
A.When the programmer needs to ensure that the answer is 100% perfect every single time.
B.When finding an exact solution to a problem would take an unreasonable amount of time (e.g., thousands of years).
C.When the computer running the program has a very small amount of disk space.
D.When the problem involves simple addition of a list of ten small integers.
B.When finding an exact solution to a problem would take an unreasonable amount of time (e.g., thousands of years).
Heuristics provide 'good enough' or approximate solutions when an exhaustive search for the optimal solution is computationally too expensive.
A computer processor executes operations of a computer program. A certain computer has two processors that are able to run in parallel. The following table indicates the amount of time it takes either processor to execute each of two processes. Assume that neither process is dependent on the other.

Which of the following best approximates the amount of time saved by running the processes in parallel instead of running them sequentially?
A. 10 seconds
B. 30 seconds
C. 40 seconds
D. 50 seconds
Running the processes sequentially (one after the other) takes 50 seconds. Running the processes in parallel takes 40 seconds because both processes start at the same time and are both finished by the time process F finishes. The amount of time saved by running the processes in parallel is 50 - 40 = 10 seconds
The following question uses a robot in a grid of squares. The robot is represented as a triangle, which is facing toward the top of the grid. The robot can move into a white or a gray square but cannot move into a black region.
Which of the following code segments can be used to move the robot to the gray square? Select two answers?
I
II.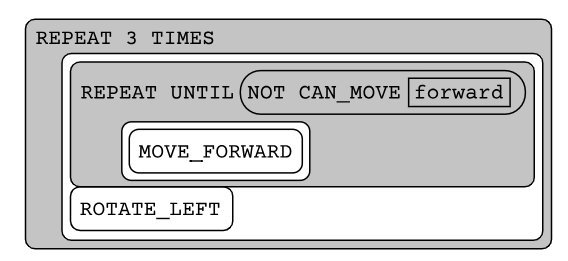
III.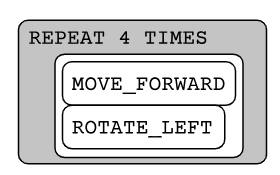
IV.
I. & II
In code segment I, the inner loop moves the robot forward four squares and then rotates it left. In code segment II the outer loop repeats the inner loop 3 times, moving the robot around the perimeter of the grid to the gray square
An Internet user requests a large file from an online media storage website. Describe how the file is transmitted to the user and name the entity responsible for establishing the protocol.
The Internet Engineering Task Force established the Transmission Control Protocol that outlines the guidelines on how a file is broken into packets that contain reassembly metadata, and these packets are routed along potentially different paths and reassembled by the recipient’s device using the metadata.
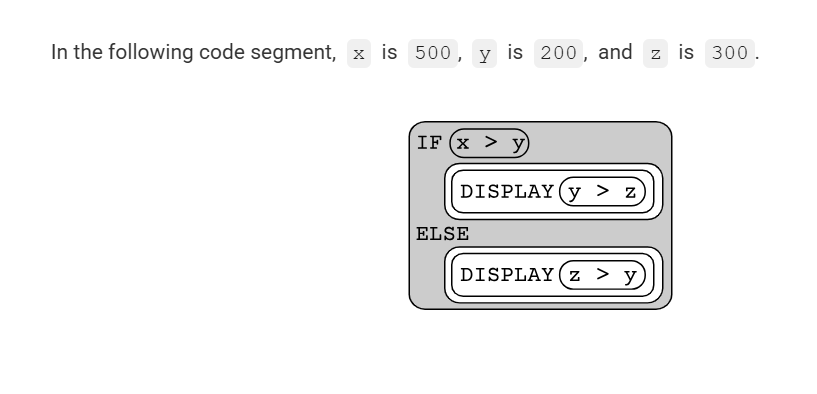
Consider the following code segment...
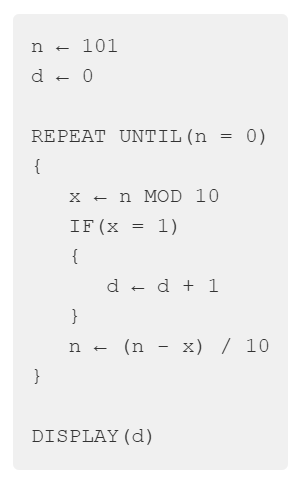
What is displayed as a result of executing the code segment?
2
The code segment counts the number of times the digit 1 appears in n. In the first iteration of the loop, x is assigned 101 MOD 10, or 1, and d is increased by 1. Then n is assigned (101 1) / 10, which is 10. In the second iteration of the loop, x is assigned 10 MOD 10, or 0, and d is unchanged. Then n is assigned (10 0) / 10, which is 1. In the third and final iteration of the loop, x is assigned 1 MOD 10, or 1, and d is increased by 1. Then n is assigned (1 1) / 10, which is 0 and the loop terminates. The code segment prints the value of d, which is 2.
What is displayed?
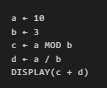
A. 4 | B. 4.33 | C. 5 | D. Approximately 4.33
C. 5
c = 10 MOD 3 = 1.
d = 10/3 = 3.33...
The sum is approximately 4.33.
In a 4-bit unsigned binary system, what happens when you add the decimal numbers 9 (binary `1001`) and 7 (binary `0111`)?
An overflow error occurs because the sum (16) cannot be represented in 4 bits.
The maximum value for 4 bits is 24−1=15. Since 16 requires 5 bits (`10000`), it causes an overflow.
In a certain country, a person must be at least 16 years old to drive a car and must be at least 18 years old to vote. The variable age represents the age of a person as an integer.
Which of the following expressions evaluates to true if the person is old enough to drive but not old enough to vote, and evaluates to false otherwise?
I. (age ≥ 16) AND (age ≤ 18)
II. (age ≥ 16) AND (NOT(age ≥ 18))
III. (age < 18) AND (NOT(age < 16))
A. I and III only
B. II and III only
C. I and II only
D. II only
B. II and III only
Incorrect - I. (age ≥ 16) AND (age ≤ 18)Includes 18. An 18-year-old can vote, so this evaluates to true for someone who is actually old enough to vote.
Correct - II. (age ≥ 16) AND (NOT(age ≥ 18))NOT(age ≥ 18) is logically equivalent to age < 18. This perfectly matches our requirements.
Correct - III. (age < 18) AND (NOT(age < 16))NOT(age < 16) is logically equivalent to age ≥ 16. This also matches our requirements, just flipped in order.
What is the purpose of the Digital Millennium Copyright Act?
A. To make all content on the Internet free for everyone to use.
B. To allow for open source software on the Internet.
C. To criminalize plagiarism on the Internet.
D. To criminalize the act of circumventing, or getting around, access controls that block access to copyrighted works.
D. To criminalize the act of circumventing, or getting around, access controls that block access to copyrighted works.
The following code segment is intended to swap the values of the integer variables x and y using the variable temp. Assume that x and y have been initialized to different integer values.
Does the code segment work as intended? What is the result of the behavior of the code segment?
The code segment does not work as intended because the value of y is changed before it is stored in x.
The following code is intended to count how many numbers in a list are between 10 and 20 (inclusive). What is wrong?

A. The loop should use indices instead of FOR EACH | B. The condition excludes 10 and 20 but should include them
C. The count variable should start at 1 | D. AND should be replaced with OR
B. The condition excludes 10 and 20 but should include them
The condition uses > and <, which excludes 10 and 20. For inclusive, it should be >= and <=.
A programmer has developed an algorithm to solve a problem for a customer. The programmer has analyzed the algorithm and found some instances of the problem for which the algorithm provides a solution and some instances of the problem for which the algorithm can never provide a solution. Assume that there are no logic errors in the algorithm.
What is the most likely explanation for the behavior of the algorithm?
The algorithm is attempting to solve an undecidable problem.
Biologists often attach tracking collars to wild animals. For each animal, the following geolocation data is collected at frequent intervals. The time, The date, The location of the animal.
Which of the following questions about a particular animal could NOT be answered using only the data collected from the tracking collars?
A. Approximately how many miles did the animal travel in one week?
B. In what geographic locations does the animal typically travel?
C. Do the movement patterns of the animal vary according to the weather?
D. Does the animal travel in groups with other tracked animals?
C. Do the movement patterns of the animal vary according to the weather?
The IPv6 protocol is the most recent version of the Internet Protocol (IP). IPv6 includes several new features related to both addressing and routing. Which of the following features of IPv6 most directly increases the scalability of the Internet?
A. The IPv6 packet includes extension headers, a way to extend the protocol to support future features that do not yet exist in the protocol.
B. The IP v6 protocol strongly recommends the use of IPSec, a protocol that adds a layer of encryption to IP packets.
C. The IPv6 header puts the most important information at the very beginning and moves the less important information to the end, enabling routers to more quickly decide how to forward packets.
D. The IPv6 header includes a way to specify which flow a packet belongs to. That can be used by routers to handle the packets for particular flows differently from packets in other flows, such as prioritizing a flow for a real-time application.
E. Each IPv6 address is a 128-bit number. That means there are 2^128 (3.4 times 10^38) possible addresses for Internet-connected computing devices.
E. Each IPv6 address is a 128-bit number. That means there are 2^128 (3.4 times 10^38) possible addresses for Internet-connected computing devices.
The scalability of a system is its capacity to change in size and scale to meet new demands. The Internet can scale to accomodate increasing numbers of Internet-connected devices by using the IPv6 addressing scheme
The program below is intended to count and display the number of integers between 1 and 100 (including 1 and 100) that are divisible by 2 or divisible by 7. The program does not work as intended.
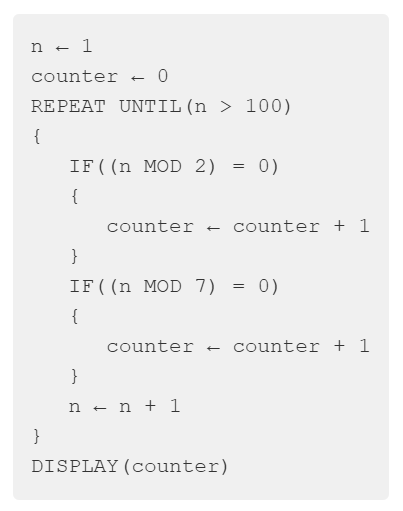
A. The value displayed is 0 because no values are counted.
B. The value displayed is greater than 0 but less than the intended result because some values are not counted.
C. The value displayed is greater than the intended result because some values are counted more than once.
D. No value is displayed because the program enters an infinite loop.
C. The value displayed is greater than the intended result because some values are counted more than once.
The code segment increments counter when n is a multiple of 2 and when n is a multiple of 7. For each number that is both a multiple of 2 and 7 (like 14 or 28), counter is incremented twice, once for each IF statement. This leads to the overall count being more than intended.