Who is this?

Who is Luigi?
CWIT stands for?
What is the Center for Women in Technology?
What does this image represent?

What is a firewall?
You enter a public place and join the public wifi what do you do?
a) Join wifi, go online and use it freely
b) Join wifi and go to Instagram
c) Join wifi and establish a VPN connection
d) Join wifi and open your bank account
What is join wifi and establish a VPN connection?
What symbol should you always make sure is present when browsing online?
Padlock symbol
![]()
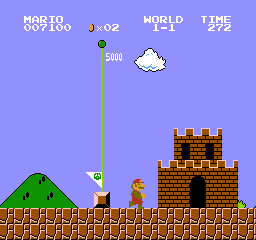
Which character is not an enemy?
a) Piranha Plant?
b) Wiggler?
c) Toad?
d) Hammer Bro?
Who is Toad?
The age of CWIT?
What is 25?
1.What is the term for a malicious software that disguises itself as legitimate software to deceive users and gain unauthorized access?
A. Malware
B. Trojanware
C. Ransomware
D. Rootkit
What is Trojanware?
What do you consider to be a good password?
a) Mario@MushroomKingdom
b) H3lloWorld
c) Collect@coins1056
d) ILovePrincessPeach2
What is Collect@coins1056?
In Super Mario bros, what type of building is always at the end of each level?
Fortress
Which character can be ridden?
a) Boo
b) Toad
c) Yoshi
d) Koopa Troopa
Who is Yoshi?
The location of the CWIT office?
Where is ITE 456?
A word or phrase that verifies that you and only you had access to the account.
What is a Password?
Which of these are a sign of a malware infection?
a) Facebook and Google show you similar ads.
b) A specific site with numerous ads appears every time you open your browser.
c) A website keeps playing a video ad every time you visit.
What is a specific site with numerous ads appears every time you open your browser?

What happens to the player when they use this power-up (Name at least 1-2)
Transforms Mario(or player) into Mini Mario
allowing him to walk on water,
make floaty jumps
enter tiny passages.
can also walk on walls
Which is not a real world in Mario games?
1) Water Land
2) Ice Land
3) Pipe Land
4) Peach Land
Where is Peach Land?
The Associate Director of CWIT?
Who is Tuesday Barnes?
A process used to enhance the security of online accounts when signing in.
What is Multi-factor authentication?
What is the most common delivery method for viruses?
a) Email attachments
b) Instant Messages
c) Internet download
d) Portable media
e) Door handles
What is Email attachments?
What is the first thing you should do if your company is facing ransomware demands?
Contact the police and do not pay the ransom.
Which was the first console to have a Super Mario game?
What is Nintendo Entertainment System (NES)?
The four values that CWIT focuses on?
What is Academic, Professional, Personal, and Inclusive Excellence?
What is the most secure symmetric encryption algorithm used today?
What is AES-256
What are warning signs to identify when you are sent a suspicious email? (name at least 3/5)
Certainly! When evaluating an email for suspicious activity, keep an eye out for the following warning signs:
Subject Lines:
- Be cautious of alarming subject lines that use words like “Urgent” or “Action Required.” Cybercriminals often employ urgency to manipulate recipients into taking hasty actions1.
Sender’s Address and Name:
- Check the domain name carefully. Look for any spelling mistakes, unusual domains, or mismatched names. Be wary of public domain email addresses or unfamiliar top-level domains2.
Generic or Overly Personalized Greetings:
- Phishing emails often use generic salutations like “Dear valued member,” “Dear account holder,” or “Dear customer.” Legitimate companies usually address you by your name. However, some hackers avoid salutations altogether3.
Grammar and Spelling Mistakes:
- Bad grammar can. Legitimate organizations typically send well-written emails. Hackers may intentionally use poor syntax to target less observant individuals3.
Requests for Sensitive Information:
- Be suspicious if an email asks for sensitive data such as passwords, credit card information, or tax numbers.
What was previous theme of the last CWIT Escape Room ?
Alien Invasion
