Art or Science?
Consider the following statements about procedural abstraction:
- It allows programmers to use a procedure without knowing the details of its implementation.
- It always improves the runtime efficiency of a program.
- It helps manage complexity in large programs by breaking them into smaller, reusable parts.
Which of the statements above are TRUE?
A. I only
B. II only
C. I and III only
D. I, II, and III
I is TRUE (abstraction hides implementation). I
I is FALSE (abstraction helps organization, not necessarily speed).
III is TRUE (breaks programs into manageable parts). Answer: I and III only.
Consider the Boolean expression: `(NOT A) AND (B OR C)`.
If `A = true`, `B = true`, and `C = false`, what does the expression evaluate to?
A.The expression is invalid due to nested operators.
B.It depends on whether the language uses short-circuit evaluation.
C.`false`
D.`true`
C.`false`
If A is true, `NOT A` is false. Since the overall expression is an `AND` between `NOT A` and the rest, a false value in either part makes the entire expression false.
When a message is sent over the Internet, it is broken into packets. What information is typically included in the 'header' of each packet?
The IP addresses of both the sender and the destination.
Headers provide the necessary routing information for routers to move the packet toward its target.
A researcher conducting an experiment has a need to generate a random number. The researcher decides to flip 5 coins and interpret heads as the binary digit 1 and tails as the binary digit 0.
How many different 5-digit binary numbers are possible as a result of the coin flips?
A. 5
B. 10
C. 16
D. 32 D Answer D Correct. The coin flips will produce a 5-bit binary number. The total number of binary numbers that can be represented using 5 bits is , or 32. The binary numbers in the range 00000 to 11111 are equivalent to the decimal numbers in the range 0 to 31
D. 32
The coin flips will produce a 5-bit binary number. The total number of binary numbers that can be represented using 5 bits is , or 32. The binary numbers in the range 00000 to 11111 are equivalent to the decimal numbers in the range 0 to 31.
A programmer is writing a script to process a list of n items. They replace a nested loop (quadratic time) with a single loop (linear time). How does this affect the 'scalability' of the program?
The program becomes more scalable because it can handle much larger lists without a massive increase in execution time.
Scalability is the ability of a system to handle growing amounts of work or data efficiently.
If a computer system uses 6 bits to represent unsigned integers, what is the maximum decimal value that can be represented?
A 6 bit system can represent 2^6(64) unique values, ranging from 0 - 2^6.
What value is displayed when the following code executes?

A. 3 | B. 6 | C. 9 | D. 12
B. 6
i=1: j runs 1 time (total=1).
i=2: j runs 1,2 times (total=3).
i=3: j runs 1,2,3 times (total=6).
Total = 1+2+3 = 6.
Which protocol is primarily responsible for breaking data into packets and ensuring they are reassembled in the correct order at the destination?
TCP (Transmission Control Protocol)
TCP provides reliable, ordered, and error-checked delivery of a stream of data packets.
Which of the following is an example of a 'Social Engineering' attack?
A.A computer script automatically tries millions of different character combinations to guess a password.
B.A server crashes because it cannot handle 50,000 simultaneous requests.
C.A hacker uses a vulnerability in a web browser to install malware without the user clicking anything.
D.A person receives a fake email from their 'bank' asking them to log in to verify their password.
D.A person receives a fake email from their 'bank' asking them to log in to verify their password.
What is the primary difference between a 'Sequential' program and a 'Parallel' program?
Sequential programs execute one instruction at a time, while parallel programs execute multiple instructions simultaneously.
Parallelism uses multiple processors to speed up execution by solving different parts of a problem at the same time.
Which of the following best explains why an overflow error might occur in a program that calculates the product of two large integers?
A.The program attempted to divide a number by zero.
B.The variable was not declared as a floating-point number.
C.The result of the calculation requires more bits than the system has allocated for integer storage.
D.The computer used lossy compression on the variable data.
The result of the calculation requires more bits that the system has allocated for integer storage.
What is the value of result after the following code executes?

A. "CMUE" | B. "OPTR" | C. "COMPUTER" | D. "CMTR"
A. "CMUE"
COMPUTER has indices 1-8.
Odd indices (1,3,5,7) give characters C,M,U,E.
Result = "CMUE".
Describe 'crowdsourcing'?
Obtaining input, ideas, or services from a large, undefined group of people, usually via the internet.
What type of error does the following code contain?
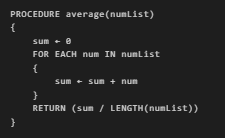
Runtime error - division by zero if list is empty
What is displayed?
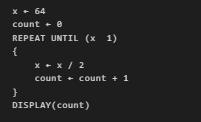
A. 5 | B. 6 | C. 7 | D. 32
B. 6
64 -> 32 -> 16 -> 8 -> 4 -> 2 -> 1. Six divisions. Count = 6.
A developer is choosing between lossy and lossless compression for a high-definition movie archive. Which statement correctly describes a trade-off of using lossless compression?
A. It reduces the file size significantly more than lossy compression by removing imperceptible details.
B. It can only be used for text-based data, not for images or video.
C. It is generally faster to transmit over the internet than lossy files.
D. It preserves the original data perfectly but results in larger file sizes compared to lossy compression.
D. It preserves the original data perfectly but results in larger file sizes compared to lossy compression.
A robot is in a 5x5 grid, starting at position (1, 1) facing right. The following commands are available: MOVE_FORWARD(), ROTATE_LEFT(), ROTATE_RIGHT().
What is the robot's position after executing this code?

A. (3, 3) facing left | B. (3, 3) facing up
C. (5, 3) facing up | D. (3, 5) facing left
A. (3, 3) facing left
Start (1,1) facing right. Move 2 right to (3,1), rotate left (facing up). Move 2 up to (3,3), rotate left (facing left). Position: (3,3) facing left.
Which of the following is a risk associated with using a single password for all of your online accounts?
A.The internet will run more slowly for you because of the lack of variety.
B.If one account is breached, the attacker can use those credentials to access all of your other accounts.
C.Your password will be converted from binary to hexadecimal by hackers.
D.The password will eventually overflow the system's memory.
B.If one account is breached, the attacker can use those credentials to access all of your other accounts.
A programmer is using an iterative loop to search for a name in a list of 500 entries. What is the maximum number of comparisons the program will make if it uses a basic linear search?
500 - In a linear search, the target might be at the very end of the list or not in the list at all, requiring a check of every single item.
Which correctly represents the iterative development process?
A. Design, Code, Test, Deploy, Never modify
B. Plan, Develop, Test, Refine, Repeat
C. Write all code first, then test everything at the end
D. Test, Code, Design, Deploy
B. Plan, Develop, Test, Refine, Repeat
Iterative development: Plan, Develop, Test, Refine, Repeat.
Which of the following is true about the way data is routed across the Internet?
A.Data is only sent through a direct physical wire that connects the sender and the receiver.
B.All packets in a single message are required to follow the exact same path to the destination.
C.The path a packet takes is determined dynamically and may change based on network congestion or link failures.
D.A central server at the Internet's 'backbone' dictates the path for every packet sent globally.
C.The path a packet takes is determined dynamically and may change based on network congestion or link failures.
Consider the following code segment:

What is displayed? (Assume 1-based indexing where REMOVE removes the element at that index)
A. [10, 25, 30, 40, 50] | B. [10, 20, 25, 30, 40, 50]
C. [10, 25, 40, 50] | D. [25, 10, 30, 40, 50]
A. [10, 25, 30, 40, 50]
Start: [10,20,30,40]. REMOVE index 2: [10,30,40]. INSERT 25 at index 2: [10,25,30,40]. APPEND 50: [10,25,30,40,50].
A network has multiple paths between any two computers. This design principle is called:
Redundancy
Which of the following is a potential negative impact of automation in the manufacturing industry?
Job displacement for workers whose tasks are now performed by robots.
While automation increases efficiency, it often leads to a reduction in human labor needed for repetitive tasks.
When you use a Creative Commons license that includes the 'Attribute' (BY) requirement, what must a person do if they want to use your work?
They must give you credit as the original creator of the work.
The 'BY' or Attribution requirement ensures the original creator is recognized when their work is reused.