Which of the following can best protect against an employee inadvertently installing malware on a company system?
A. Host-based firewall
B. System isolation
C. Least privilege
D. Application allow list
D: What is Application allow list
After a security awareness training session, a user called the IT help desk and reported a suspicious call. The suspicious caller stated that the Chief Financial Officer wanted credit card information in order to close an invoice. Which of the following topics did the user recognize from the training?
A. Insider threat
B. Email phishing
C. Social engineering
D. Executive whaling
C: What is Social engineering
A systems administrator wants to prevent users from being able to access data based on their responsibilities. The administrator also wants to apply the required access structure via a simplified format. Which of the following should the administrator apply to the site recovery resource group?
A. RBAC
B. ACL
C. SAML
D. GPO
A: What is RBAC
Which of the following security concepts is the best reason for permissions on a human resources fileshare to follow the principle of least privilege?
A. Integrity
B. Availability
C. Confidentiality
D. Non-repudiation
C: What is Confidentiality
After reviewing the following vulnerability scanning report:

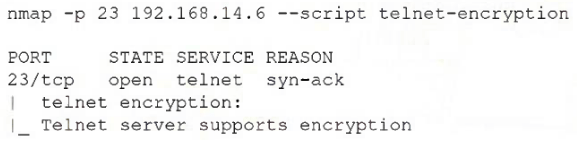
A security analyst performs the following test:
Which of the following would the security analyst conclude for this reported vulnerability?
A. It is a false positive.
B. A rescan is required.
C. It is considered noise.
D. Compensating controls exist.
A: What is It is a false positive.
A security administrator is deploying a DLP solution to prevent the exfiltration of sensitive customer data. Which of the following should the administrator do first?
A. Block access to cloud storage websites.
B. Create a rule to block outgoing email attachments.
C. Apply classifications to the data.
D. Remove all user permissions from shares on the file server.
C: What is Apply classifications to the data.
An employee receives a text message from an unknown number claiming to be the company’s Chief Executive Officer and asking the employee to purchase several gift cards. Which of the following types of attacks does this describe?
A. Vishing
B. Smishing
C. Pretexting
D. Phishing
B: What is Smishing
A network manager wants to protect the company's VPN by implementing multifactor authentication that uses:
Something you know
Something you have
Something you are
Which of the following would accomplish the manager's goal?
A. Domain name, PKI, GeoIP lookup
B. VPN IP address, company ID, facial structure
C. Password, authentication token, thumbprint
D. Company URL, TLS certificate, home address
C: What is Password, authentication token, thumbprint
An administrator assists the legal and compliance team with ensuring information about customer transactions is archived for the proper time period. Which of the following data policies is the administrator carrying out?
A. Compromise
B. Retention
C. Analysis
D. Transfer
E. Inventory
B: What is Retention
A company is working with a vendor to perform a penetration test. Which of the following includes an estimate about the number of hours required to complete the engagement?
A. SOW
B. BPA
C. SLA
D. NDA
A: What is SOW
After an audit, an administrator discovers all users have access to confidential data on a file server. Which of the following should the administrator use to restrict access to the data quickly?
A. Group Policy
B. Content filtering
C. Data loss prevention
D. Access control lists
D: What is Access control lists
Malware spread across a company's network after an employee visited a compromised industry blog. Which of the following best describes this type of attack?
A. Impersonation
B. Disinformation
C. Watering-hole
D. Smishing
C: What is Watering-hole
The local administrator account for a company's VPN appliance was unexpectedly used to log in to the remote management interface. Which of the following would have most likely prevented this from happening?
A. Using least privilege
B. Changing the default password
C. Assigning individual user IDs
D. Reviewing logs more frequently
B: What is Changing the default password
A company is required to perform a risk assessment on an annual basis. Which of the following types of risk assessments does this requirement describe?
A. Continuous
B. Ad hoc
C. Recurring
D. One time
C: What is Recurring
An organization is struggling with scaling issues on its VPN concentrator and internet circuit due to remote work. The organization is looking for a software solution that will allow it to reduce traffic on the VPN and internet circuit, while still providing encrypted tunnel access to the data center and monitoring of remote employee internet traffic. Which of the following will help achieve these objectives?
A. Deploying a SASE solution to remote employees
B. Building a load-balanced VPN solution with redundant internet
C. Purchasing a low-cost SD-WAN solution for VPN traffic
D. Using a cloud provider to create additional VPN concentrators
A: What is Deploying a SASE solution to remote employees
Which of the following describes a security alerting and monitoring tool that collects
system, application, and network logs from multiple sources in a centralized system?
A. SIEM
B. DLP
C. IDS
D. SNMP
A: What is SIEM
Which of the following vulnerabilities is exploited when an attacker overwrites a register with a malicious address?
A. VM escape
B. SQL injection
C. Buffer overflow
D. Race condition
C: What is Buffer overflow
During the onboarding process, an employee needs to create a password for an intranet account. The password must include ten characters, numbers, and letters, and two special characters. Once the password is created, the company will grant the employee access to other company-owned websites based on the intranet profile. Which of the following access management concepts is the company most likely using to safeguard intranet accounts and grant access to multiple sites based on a user's intranet account?
(Choose two.)
A. Federation
B. Identity proofing
C. Password complexity
D. Default password changes
E. Password manager
F. Open authentication
A and C: What is Federation and Password complexity
Which of the following is the best reason to complete an audit in a banking environment?
A. Regulatory requirement
B. Organizational change
C. Self-assessment requirement
D. Service-level requirement
A: What is Regulatory requirement
A newly identified network access vulnerability has been found in the OS of legacy IoT devices. Which of the following would best mitigate this vulnerability quickly?
A. Insurance
B. Patching
C. Segmentation
D. Replacement
C: What is Segmentation
A company must ensure sensitive data at rest is rendered unreadable. Which of the following will the company most likely use?
A. Hashing
B. Tokenization
C. Encryption
D. Segmentation
C: What is Encryption
A company's end users are reporting that they are unable to reach external websites. After reviewing the performance data for the DNS severs, the analyst discovers that the CPU, disk, and memory usage are minimal, but the network interface is flooded with inbound traffic. Network logs show only a small number of DNS queries sent to this server. Which of the following best describes what the security analyst is seeing?
A. Concurrent session usage
B. Secure DNS cryptographic downgrade
C. On-path resource consumption
D. Reflected denial of service
D: What is Reflected denial of service
Which of the following risk management strategies should an enterprise adopt first if a legacy application is critical to business operations and there are preventative controls that are not yet implemented?
A. Mitigate
B. Accept
C. Transfer
D. Avoid
A: What is Mitigate
After a company was compromised, customers initiated a lawsuit. The company's attorneys have requested that the security team initiate a legal hold in response to the lawsuit. Which of the following describes the action the security team will most likely be required to take?
A. Retain the emails between the security team and affected customers for 30 days.
B. Retain any communications related to the security breach until further notice.
C. Retain any communications between security members during the breach response.
D. Retain all emails from the company to affected customers for an indefinite period of time.
B: What is Retain any communications related to the security breach until further notice.