This term refers to the physical parts of a computer that you can touch and see, such as the monitor, keyboard, and mouse.
Hardware
A legal term referring to the rights given to creators for their literary and artistic works, preventing others from copying them without permission.
Copyright
This is a secret combination of characters used to verify your identity; a strong one should include a mix of letters, numbers, and symbols.
Password
A software application used to access and view websites on the Internet (e.g., Chrome, Firefox, Safari)
Web Browser
HTML stands for this.
HyperText Markup Language
This type of data representation uses only two states (on/off) and is the lowest level of abstraction in a computer.
binary
This component is often called the "brain" of the computer because it processes instructions and calculations.
CPU/Processor
A recognizable symbol, word, or design established by use as representing a company or product (e.g., the Nike Swoosh).
Trademark
An attempt to trick users into revealing sensitive information, like passwords or credit card numbers, often via fake emails. (must be specific)
Phishing
A unique string of numbers separated by periods that identifies each computer using the Internet Protocol to communicate over a network.
IP Address
The HTML tag used to create the largest size<h1> heading
<h1>
Binary 10101 in decimal.
21
This type of memory is "volatile," meaning it loses all its data when the computer is turned off.
RAM/Memory
The act of taking someone else's work or ideas and passing them off as your own.
Plagiarism
Malicious software designed to harm or exploit any programmable device, service, or network.
Malware
Small chunks of information that have been carefully formed from larger chunks of information for transmission across the Internet.
Packets
The meanings of <ul>, <ol>, and <li>
Unordered List, Ordered List, and List Item
This 7-bit encoding system was designed to represent English characters as numbers.
ASCII
A persistent storage device that uses no moving parts and is faster than a traditional hard disk drive.
SSD (Solid State Drive)
Software where the original source code is made freely available and may be redistributed and modified.
Open-Source Software
A form of malware where the attacked encrypts your files and demands payment.
Ransomware
This system translates human-friendly domain names (like https://www.google.com/) into IP addresses that computers use. (the acronym is only half points)
Domain Name Server (DNS)
The meaning of <hr> and what it creates on the page
Horizontal Rule - horizontal line (AKA rule) across the page
Decimal 97 in binary.
1100001
The main circuit board that connects all the other components of the computer together, allowing them to communicate.
Motherboard (Mobo)
A type of public copyright license that allows creators to give permission for others to share and use their work under specific conditions.
CC - Creative Commons
A security feature that requires two or more forms of identification to access an account (e.g., a password and a code sent to your phone).
Multi-Factor Authentication (MFA)
A design feature of the Internet that allows it to continue operating properly in the event of the failure of some of its components (like a broken wire).
Fault Tolerance (or Redundancy)
This is the complete line of code at the very top of any HTML document (include any capitalization, punctuation, etc)
<!DOCTYPE HTML>
The shape this code draws when the green flag is pressed:
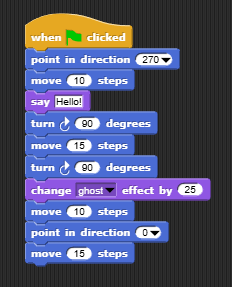
square
Name a device that can act as an input and an output.
Answers may vary.
The length of a copyright.
Life of the author + 70 years
Self-replicating malware that can spread itself without you intervening.
Worm
This kind of animal has been known to cause Internet outages by damaging the cables running through its habitat.
Shark
The minimum, complete line of code you need to display an image called six-seven.jpg on a webpage (include capitalization, punctuation, etc)
<img src="six-seven.jpg">
In the RGB color model, what color is produced by the value (255, 100, 0)?
Orange
This type of storage is neither magnetic nor flash and is dying out, but you likely still have many forms of this at home.
Optical (CDs, DVDs)
The year in which copyright length was most recently modified.
1978
A type of attack where multiple compromised computer systems attack a target, such as a server or website, to cause a denial of service for users.
DDOS Attack
The primary protocol used for transmitting data across the Internet that ensures packets arrive in order and without error. (acronym is half points)
TCP (Transmission Control Protocol)
The complete line of code needed to create this red paragraph text:

<p style="color:red;">Hello, World!</p>
The decimal number 16 in ternary
121